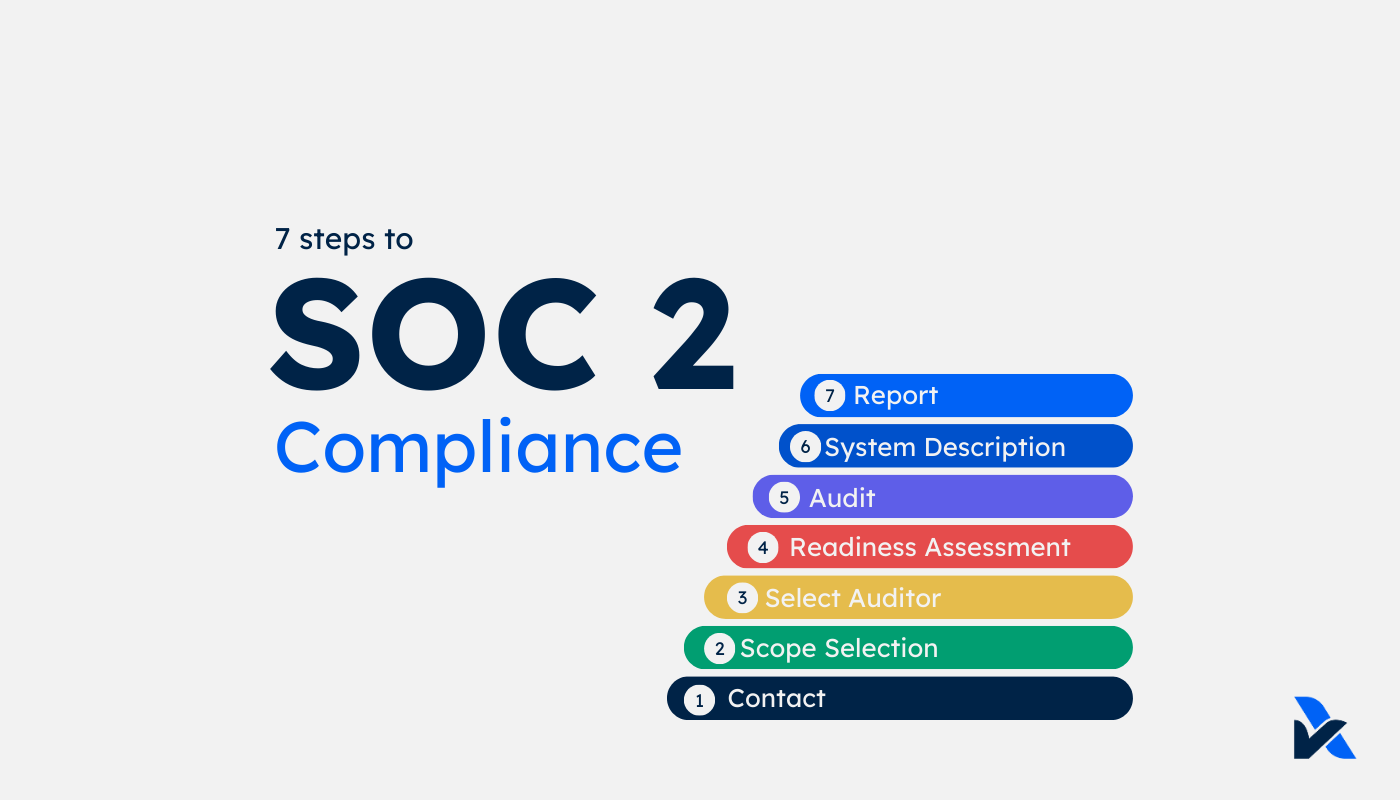
The 7 Steps to SOC 2
Security threats have never been more prevalent. Companies are differentiated from their competitors by their commitment to sound security practices and the ability to demonstrate those practices. There's 7 steps that achieve and report on SOC 2 to open new business opportunities and scale with confidence.
Updated: Feb 16
There are seven (7) steps to achieve and report on SOC 2 compliance with the AICPA Trust Services Criteria.
Step 1: Contact a SOC 2 Provider
It's easy to get lost in all the terminology and standards. It can be difficult and confusing to know which standard suits your needs best and what's actually required to achieve compliance. Save yourself time and contact one or more providers - let them guide you on what's relevant to you.
Step 2: SOC 2 Scope Selection
Whether it's ISO 27001, SOC 2, or other standards, you need to determine the scope that applies. This is what the end user requires assurance over. The services, systems and criteria that apply.
For example, your company may have multiple entities and types of services. You don't need to include all of those if they aren't relevant to the end users' requirements. ISO 27001 reports over Security only, whereas for SOC 2, there are five Trust Services Principles; Security, Availability, Confidentiality, Privacy and Processing Integrity.
If this is getting confusing, don't sweat. AssuranceLab has a free and easy
Readiness Assessment to get started.
Step 3: SOC 2 Service Auditor & Approach
There's often hesitation to select an auditor and approach. It can be daunting when there are a lot of unknowns for what's to come. But without a decision, there's a lack of clarity in how to proceed, which results in a standstill.
What you decide initially is less important than it seems. You can change approach or even service providers if you need to. At AssuranceLab, our terms never lock you in. About 30% of our clients have changed the approach or scope of their reports, some within days of issuing the SOC 2 report. We have had clients switch to our services from other providers. Despite perceptions, the actual barriers for switching are low.
What you need to select, is which provider to proceed to Step 4 with, and whether you will initially pursue SOC 2 Type 1 or straight to SOC 2 Type 2. Read our comparison of SOC 2 Type 1 & SOC 2 Type 2.
Step 4: SOC 2 Readiness Assessment
The Readiness Assessment is like a pre-audit check to prepare you for the audit, or to confirm that you are well positioned for it. It identifies any observations of potential non-compliance with the criteria, and the practices you perform that are required for compliance. AssuranceLab's SOC 2 Readiness Assessment App uses an automated and personalised assessment process. The Readiness Assessment prepares:
- A list of any observations with recommendations;
- Your "control" practices that satisfy the criteria; and
- The audit evidence required and auditors' test procedures, so there's complete transparency of what's required for the audit.
Step 5: Audit
Unlike a tax or financial audit, SOC 2 and ISO 27001 audits are not trying to catch you out. The auditor is seeking documentation or other evidence to prove that your practices are what you say they are. For SOC 2 Type 2, the auditor also verifies that you are actually applying the practices in line with how you say you are (termed "operating effectiveness").
Typically for SOC 2 there's an average of ~85 unique "controls" that require an average of 100 "evidence requests" to prove them. For ISO 27001 there's 144 standard controls, with about 80 mandatory documents and records to be evidenced that are typically more prescribed but also more comprehensive.
Step 6: SOC 2 System Description
SOC 2 is an "attestation" report, rather than a certification like ISO 27001. For all intents and purposes, most end users see these as the same thing. The key difference is that SOC 2 requires a System Description that sets out the scope, a description of the relevant processes and company practices, and lists the controls and auditor validation procedures.
SOC 2 is less prescriptive than ISO 27001, so this is important for end users to consider whether they are satisfied with the practices that are applied to their services. It also includes complementary user entity and sub-service organisation controls so that users can understand what is and isn't covered by the report with respect to the user's own responsibilities and key vendors used in providing the services (eg, Infrastructure providers) that are not included in the scope.
Step 7: Report Issuance
The report is formally issued to you, the Service Organisation. This is your responsibility to share with customers as you see fit, but comes with terms that it needs to be shared in an appropriate manner, eg, not in an incomplete form or other manner that may be deceptive to the end users about its purpose, scope and auditor's opinion.
There you have it, seven easy steps to achieve and issue a report on your SOC 2 compliance. Most Service Organisations that make it through, continue issuing SOC 2 reports annually. Whether that's to continue to demonstrate their compliance to end users, or some even find it helps manage their organisation, applies consistency that enables successful operations and provides an ongoing framework for improvement and empowerment of your teams.
To read more about SOC 2, check out our other articles: